If you’re wondering “how to block hackers from my phone,” or what you’ve come to the right place. In this article, we’ll cover seven easy-to-follow tips that will help you to protect your phone from hackers.
Key Notes
- Keep up to date – and don’t open up holes yourself.
- Be careful of what you install.
- Review what’s already on your phone.
- Make it hard for intruders to get in.
- Be prepared to track and lock your phone.
- Don’t leave online services unlocked.
- Adopt an alter ego.
- Beware of open wifi.
- Lock individual apps.
- Get a warning when your phone goes walkies.
- Keep an eye on things behind the scenes.
- Keep Your Tracking and Remote Locking Settings On.
- Install Security Software Tools on Your Mobile Device.
- Be Judicious About What You Download and Install on Your Phone.
- Protect Yourself from SIM Swapping.
- Additional Tips on How to Protect Your Phone from Hackers.
I’d also strongly advise against using unofficial tools to “root” your phone (known as “jailbreaking” on iOS) unless you know exactly what you’re doing. On a rooted phone, technical safeguards can be defeated, allowing apps to perform all sorts of actions that are normally prohibited – and that can include snooping on your personal data.
2. Be careful of what you install:
When you install a smartphone app, you may be asked to grant it various permissions, including the ability to read your files, access your camera or listen in to your microphone. There are legitimate uses for these capabilities, but they’re potentially open to abuse: think before you approve the request. That applies especially to Android users, as Google’s app-vetting process isn’t as strict as Apple’s, and there have been reports of malicious apps spending months on the Play Store before being spotted and taken down.
Android also lets you install apps from third-party sources: this allows services such as Amazon’s competing Appstore to operate, but it also provides an easy way for rogue apps to get onto your phone. I’d strongly advise against installing anything from an unfamiliar website.
Even if the apps on your phone seemed simple and safe when you installed them, subsequent updates could have turned them into something more sinister. Take two minutes to review all the apps on your smartphone, and see which permissions they’re using: on iOS, you’ll find lots of relevant information under Settings > Privacy.
On Android, it’s harder to get an overview of which apps have which permissions, but there are plenty of security apps that help here, including free packages from Avast and McAfee. These tools can also jump in and alert you if you’re trying to install an app that’s known to be malicious, and warn you if a “phishing” attack is trying to trick you into entering a password into an untrusted app or webpage.
If a thief gets physical access to your phone, they can cause all sorts of trouble. For a start, your email app probably contains a trove of personal information. Make sure your phone is locked when not in use: both Android and iOS can be set to require a six-digit passcode. Your device may offer other options too, like fingerprints or facial recognition. Such methods aren’t perfect – a really determined hacker could copy your fingerprints from a drinking glass, or trick a camera with a photograph of you – but they’re a lot better than nothing.
And be wary of “smart unlock” features, which automatically unlock your phone when you’re at home, or when your smartwatch is near; these could let a thief bypass your unlock code altogether.
Plan, so even if your phone is stolen, you know your data is safe. One option is to set your phone to automatically erase itself after a certain number of incorrect attempts to enter the passcode.
If that seems a bit drastic, don’t forget that both Apple and Google operate “find my device” services that can locate your phone on a map, and remotely lock or erase it. For Apple users, this is accessed through the iCloud website – you can check it’s enabled on the phone in Settings > iCloud > Find My iPhone. Android users can access Google’s service at google.co.uk/android/devicemanager. You can also make a missing phone ring – helpful for drawing attention to the thief, or tracking down a handset that’s been merely mislaid.
We all know there's a risk involved in using an open wireless network. But you may not realize how severe it is
Auto-login is a very convenient feature, especially since a virtual keyboard can make typing passwords a chore. It’s also a huge liability: an intruder simply needs to open your browser to gain access to all your online accounts.
Ideally, therefore, you shouldn’t use auto-login features at all. If you must, use a password manager app that requires you to regularly re-enter a master password. And don’t use the same password for more than one app or service: if that one password gets found out, it can be used to access a whole range of private information. This applies even if you’re perfectly scrupulous about keeping your smartphone secure: hackers regularly break into online services to steal user credentials, which they then try out on other sites.
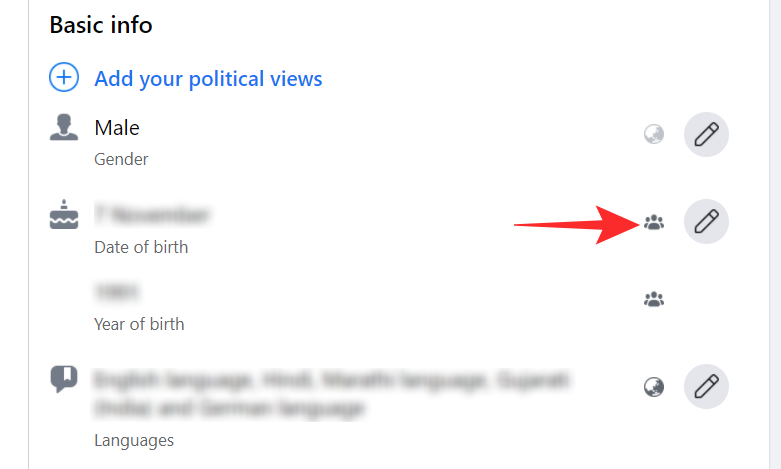
If you’ve followed this advice so far, it should be very difficult for anyone to get into your phone. However, some major hacks have been pulled off without any access to the victim at all. If someone can find out (for example) your date of birth, hometown, and mother’s maiden name – all stuff that can be easily picked up from a site like Facebook – that’s often all they need to reset a password and start breaking into your accounts. You can see off such attacks by fictionalizing your past with details that are unlikely to be guessed; perhaps, for the purposes of security, you were born in 1999 to Mrs. Victoria Beckham, née Adams. Just remember what you claimed, or you could end up locking yourself out.
Personal information can easily be gleaned from sites such as Facebook.
If you’re at all doubtful about a wireless network, don’t connect – stick with your phone’s mobile internet connection. Or use a VPN tool such as CyberGhost or TunnelBear (both available free for Android and iOS). These tools route your traffic through a private encrypted channel, so even if someone is monitoring your traffic they won’t be able to see what you’re up to.
Lots of apps pop up messages and notifications on your phone’s lock screen. It’s worth thinking about what these notifications may reveal. If you work for a big banking company, for example, a visible email from a work colleague or a meeting reminder tells a thief that this might be a particularly interesting phone to steal.
On iOS, also consider disabling access to Siri from the lock screen. Siri isn’t supposed to give away personal information before you enter your passcode to unlock the iPhone, but past hacks have let intruders use Siri to unlock the device, access details of contacts, and view photos. It’s safest to shut the feature off entirely: you’ll find the option under Settings > Touch ID & Passcode > Disable Siri on the Lockscreen.
9. Lock individual apps:
On Android, as a second line of defense, you can lock individual apps, so even if someone can get past your lock screen, they can’t open your email or banking app without a second password. This capability isn’t built into the OS, but there are plenty of free apps that provide it, such as AVG AntiVirus Free. iOS users can’t directly lock individual apps, but check out Folder Lock – free on the App Store – which can password-protect your documents and folders, reducing the amount of information a thief can access.
The device will normally be less than 50 meters away when the connection drops, so the warning gives you a chance to ring the phone right away, hopefully drawing attention to the thief and prompting them to jettison it. Failing that, you can lock it before the culprit has a chance to start trying to break in and steal your data.
Phones are an integral part of our lives. Results from reviews.org survey show that 75.4% of respondents feel that they’re addicted to their phones. Furthermore, nearly two-thirds of respondents reported checking their phones up to 160 times per day! Now, we’re not here to judge anyone’s mobile addictions, but we do want to help you understand how to protect your phone from hackers.
At this stage, we assume that you’ve enabled your mobile’s lock screen feature with a multi-digit passcode, face/fingerprint recognition, or a complicated pattern. This is particularly helpful if you lose your phone or if a thief has gotten their hands on your device. But if you think that your screen lock will make it impossible for thieves to misuse your phone, you’re not aware of the tricks hackers can use to bypass the phone’s initial security mechanism. There are ways to bypass even fingerprint lock and facial recognition security mechanisms!
This is where the ability to remotely lock your device is essential. This is the first step in protecting your phone from hackers or anyone who shouldn’t have access to your device. Fortunately, virtually all the phone providers offer to Find My Device and remote lock functionalities. You just need to install those apps (if they don’t come pre-installed on your device) and register your device.
For example, you can use the Google Find My Device app for Android phones and Find My iPhone for Apple phones. To enable these apps, choose your type of device below and follow these easy directions:
For iPhones: Go to Settings > Passwords, and Accounts > iCloud > Turn on Find My iPhone, Enable Offline Finding and Send Last Location.
For Android Phones: You just need to link your Gmail account in Google Find My Device app, and it will start working without any further settings. All the android device providers have this feature available. For Samsung phones, you can use Samsung’s Find My Mobile tool, too.
These apps also give you the ability to lock your phone remotely. If you’re sure that your phone is in the wrong hands, you can also erase your entire phone memory remotely so that no one can misuse your data. Erasing your phone is a risky step, so create regular backups of your important data.
Antivirus software and anti-malware software are not limited to computers only. You should use them on your mobile phones as well to protect your phone from hackers. When you surf online, different types of malware (like viruses, trojan horses, worms, etc.) can be installed on your device via malware-loaded websites. Your device also might get infected through malicious email attachments or apps.
Security software not only detects and removes malware but also can warn you when you visit a bad site or download a malicious app. Some malware gets downloaded on your mobile without your notice. A good security program scans and notifies you every time something downloads to your device.
With “freemium” security software, typically the basic service is free. If you want to tighten the security and need more features, you can upgrade them to a commercial service. You should check the advantages and disadvantages of both free and paid versions to determine the best solution for your device.
Not everything is as it appears. Be vigilant when installing apps or downloading images, videos, files, songs, email attachments, etc. from the internet.
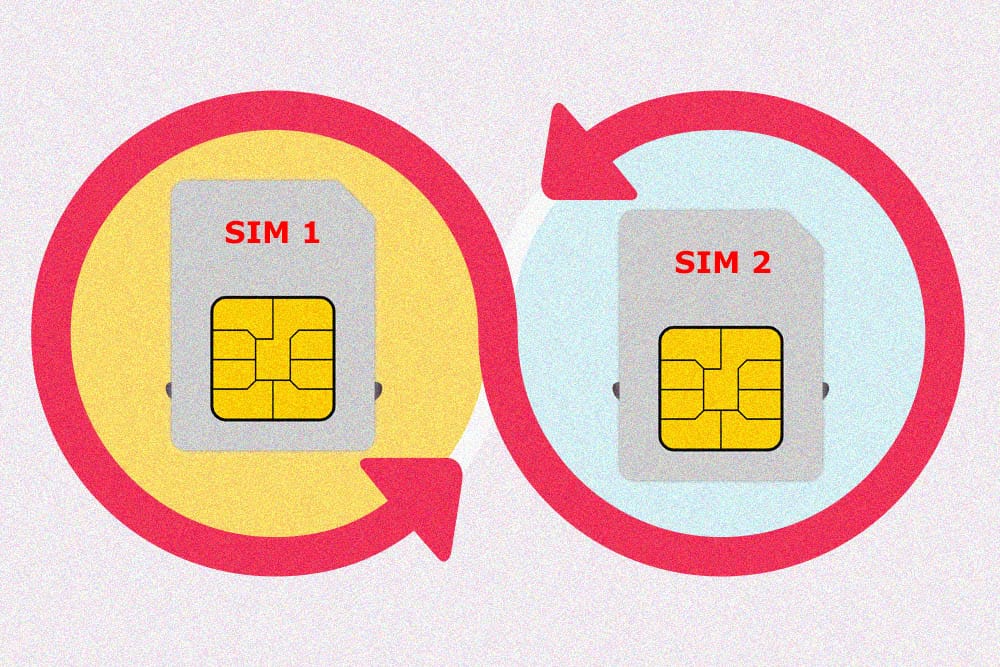
15. Protect Yourself from SIM Swapping:
SIM swapping occurs when a bad guy calls your mobile service provider and asks for a replacement SIM card. This unauthorized SIM swapping is possible when a hacker has access to some of your confidential information (such as the last four digits of your social security number, or any identity proof document) and uses it as part of their social engineering scam.
If they’re successful in convincing your mobile provider to port your number, the attacker can intercept all your phone calls, SMS text messages, and potentially gain access to all accounts and services that are linked to your phone number.
For example, if you’ve enabled a one-time password (OTP) as a part of two-factor authentication (2FA) for your bank, attackers can receive your OTP or a secret code via SMS and complete the transaction! On your end, all you’ll see is that your phone has lost service and you won’t be able to make or receive any calls.
As if all of this isn’t bad enough, perpetrators can also access all your apps (Facebook, Twitter, Linked In, etc.) in which you have used your phone number as your user ID. They just need to hit the “forgot password” links and change the passwords with the links they receive via SMS text messages.
Pro Tip: To protect yourself from unauthorized SIM swapping or number porting, set up a unique PIN or passcode with your mobile service provider. This would be a number that only you know that you have to use to access or make changes to your mobile account (including number/account porting to other devices).
You can also use apps like Google Authenticator, Authy, or Google’s code-less authentication method to add another layer of security. Apple’s two-step verification feature can send an OTP to a registered device (rather than to the phone number) whenever someone tries to log in from a new device. This adds an additional layer of non-SMS-based MFA security to your device.
In other words, even if the perpetrator inserts a replacement SIM card into a new device, they still can’t activate it until they provide the OTP, which iOS sends only to your (registered) device or to another phone number linked/connected to your primary phone number. You can also set an app-specific password, so no one can open your apps without providing those passwords.
Additional Tips on How to Protect Your Phone from Hackers
Before moving forward, let’s have a quick look at these powerful tips that will help you to protect your phone from hackers.Disable the “Allow Siri When Locked” function. Go to Settings > Siri and Search > Disable the Allow Siri When Locked feature**.** In the past, some bugs in the iPhone allowed anyone to bypass the screen lock and access a couple of functions using Siri.
Password protects your cloud storage apps. This includes apps such as Google Drive, Google Docs, iCloud, etc. Check out these resources for more information on how to protect your iCloud account and how to protect your Google Drive and docs.
Disable the “smart unlock” feature. Some mobile devices have this feature, which automatically unlocks your phone when you are at a “safe” location (home, work, etc.) or when your smartwatch is nearby. But it’s very risky because the attackers can bypass the lock screen authentication if they are in near proximity.
Password protects important files, folders, and apps from getting an additional layer of security. Use Apps like Folder Lock (available for both Android and iPhones) for this purpose.
Avoid using public charging ports. Hackers can compromise charging ports (this is known as juice jacking) to intercept the data and break into your device.
Avoid jailbreaking devices. Jailbreaking (or rooting) means making unauthorized changes in the default device settings using some software. People jailbreak their phone to unlock it (change service providers), use banned or pirated apps, customize the looks, or enable tethering (hotspot) service without paying an extra fee. But when you jailbreak your phone, you not only void the device’s warranty but also weaken the phone’s security posture. Hackers can easily insert malware and steal confidential data from a jailbroken phones.
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
*JOIN ME ON SOCIAL MEDIA*📌YouTube: https://www.youtube.com/channel/UCkdR...
📌Facebook:
📌Instagram:
📌Telegram: https://t.me/unboxingspace
📍Website: https://unboxingspace21.blogspot.com
••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••
I hope this video was Useful and you liked it if you did press the thumbs up button. & Subscribe to our Channel.
Thank you. Team US :)
••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••
E-mail us for Business & Promotion on: unboxingspace2020@gmail.com
••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••
This channel is Managed by: INFINITYgroupDM: https://bit.ly/InfinitygroupDM
===========================================================================
Credits:-
Team Pixel Creation (video production): http://bit.ly/3c2FB9d
Branding Center (graphics): http://bit.ly/3wENlWW
DOP(Shivraj Patil): http://bit.ly/3wJz6A5
Online Space (Script): https://bit.ly/2RW2pRe
All content is Copyright ©️ to Unboxing Space.
••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••••














Comments
Post a Comment